I get a lot of email, and have a copule email accounts to deal with.
One of the things I’ve done to simplify is to standardize on one
email client.
I use Alpine.
Why Alpine?
This is where anyone else would try to sell you on Alpine.
I don’t think Alpine is especially highly regarded. There are
more techie-friendly options out there – those folks like
mutt. There are easier-to-setup solutions
out there, I’m sure, too. (Office365 Web access).
I chose Alpine because I was familiar with pine (it’s predecessor) and
because I can manage my email in it quickly with keystrokes.
I’m not sure I want to sell anyone on this solution, per se.
But I am sure I don’t want to have to google how to set up
all the variables again, if I blow away my configuration.
Setup
I’m going to assume you’ve installed alpine.
This also assumes you’ve edited a .pinerc file before,
or can stumble your way through the menus inside Alpine
– within Setup (S), Config (C).
Here were the important things to edit in my .pinerc:
Remove “user.name@domain.tld” and replace with your account.
# You want emails to show your name when sent.
personal-name=Charles Mercadal
# smtp-server is the Office365 SMTP server (it sends your mail).
smtp-server=smtp.office365.com:587/tls/novalidate-cert/user=user.name@domain.tld
# set your inbox path... so going to your inbox in alpine displays the right stuff
inbox-path={outlook.office365.com/tls/novalidate-cert/user=user.name@domain.tld}INBOX
# drafts folder setup
postponed-folder={outlook.office365.com/tls/novalidate-cert/user=user.name@domain.tld}Drafts
# this one is important, if you ever want to read stuff you've deleted
# I always forget what this folder is officially called in Exchange/Office365
trash-folder={outlook.office365.com/tls/novalidate-cert/user=user.name@domain.tld}Deleted Items
# expunge-only-manually works with filters specified below to make sure
# deleted stuff gets moved to the trash folder.
# ignore-size-changes seems to be related to an Office365 bug when saving emails.
# The others are personal preference
feature-list=expunge-only-manually,
convert-dates-to-localtime,
combined-folder-display,
ignore-size-changes,
no-quell-attachment-extension-warn
# This sets the composer to send from your Office365 account
alt-addresses=user.name@domain.tld
# folder-collections pull in all your Office365 folders for viewing.
folder-collections=mail/[],
Office365 {outlook.office365.com/tls/novalidate-cert}[]
# set up roles and filters
# the filter is the one noted above, that moves deleted stuff into "Deleted Items"
patterns-roles=LIT:pattern="/NICK=Default/FLDTYPE=EMAIL" action="/ROLE=1/FROM=Charles Mercadal <user.name@domain.tld>/RTYPE=NC/FTYPE=NC/CTYPE=NC"
patterns-filters2=LIT:pattern="/NICK=Move deleted to Deleted Items/FLDTYPE=EMAIL/FOLDER=INBOX/STATD=YES" action="/FILTER=1/FOLDER={outlook.office365.com\/tls\/novalidate-cert\/user=user.name@domain.tld}Deleted Items/NOKILL=1"
That’s the important stuff to make sure your emails don’t end up
where you don’t expect them.
Other friendly stuff
You can set up a remote config if you want to be able to
use the same setup anywhere you go. I have an alias set up so
I can run this command wherever I check my email.
alpine -p '{outlook.office365.com/tls/novalidate-cert/user=user.name@domain.tld}remote_pinerc'
You can also create yourself an address book and then
add that remotely, to be used from anywhere. From the main screen,
go to setup (S) and then AddressBook (A).
Bonus: Do you like typing less?
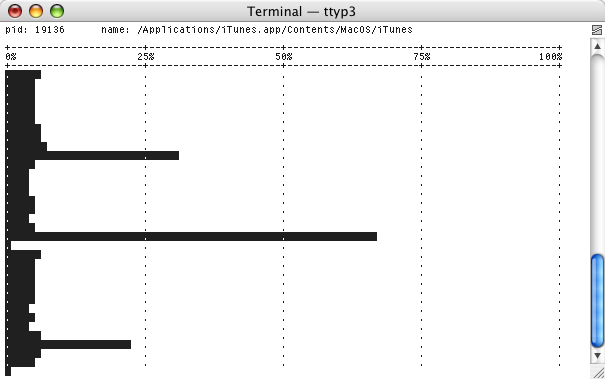
I run Alpine within tmux.
This allows me to define common keystrokes and send them through
into Alpine.
One of the things I don’t like about Alpine is when a specific item
is only available through multiple layers of menus and/or questions.
This is how I got around it.
I’ve defined a few F-keys to type repetitive things into Alpine
on my behalf. Here are a few of the highlights.
Put these in your .tmux.conf
# F10: save selected item to Downloads
# This works in a message, when looking at your attachments.
# Select an attachment and hit F10.
# It will open the file browser, search for a folder named Downloads,
# then hit return the requisite number of times to get the download to happen.
bind-key -n F10 send "S" C-t "WDownload" C-m C-m C-m C-m
# F11: save to archive
# From the message list, select a message and hit F11.
# This one moves into the message collection, looks for a folder
# named "Archive" and saves your message there.
bind-key -n F11 send "S" C-n "Archive" C-m
# F12: filter now and return to index
# After deleting/moving a bunch of messages, F12 will clean up your inbox.
# It does so by navigating the menus through:
# Main (M), Setup (S), Roles (R), FilterNow (N), and then back to Inbox (I)
bind-key -n F12 send "MSRNI"
]]>